[ad_1]
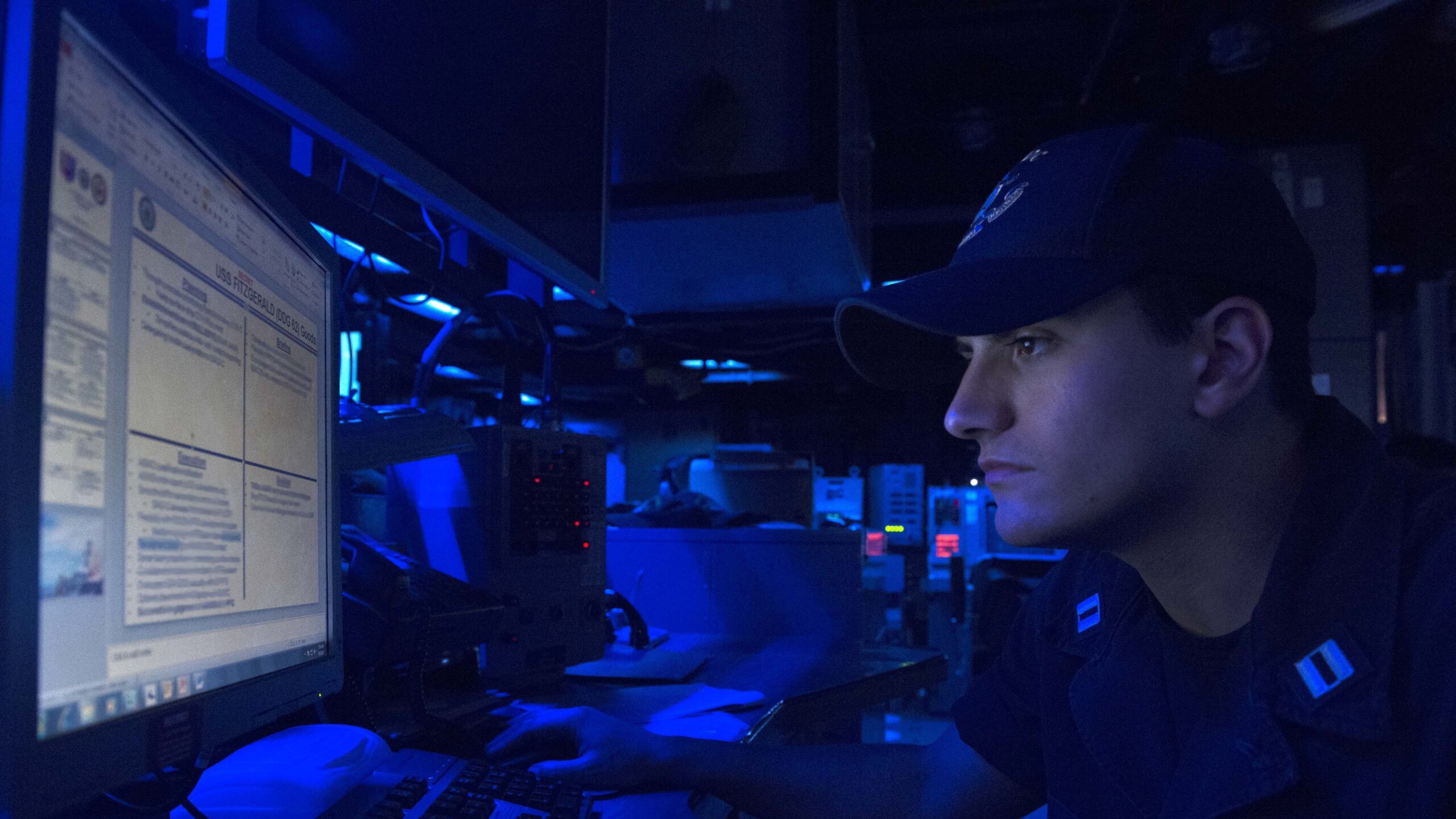
Lt. Christian Asaban sights a personal computer check aboard the forward-deployed Arleigh Burke-class guided-missile destroyer USS Fitzgerald (DDG 62) throughout Multisail 17 on March 8, 2017. (U.S. Navy photo by Mass Conversation Specialist 2nd Class William McCann/Unveiled)
WASHINGTON: The way the Navy at this time ways cybersecurity is “wrong,” and the service demands to shift from viewing it as a compliance challenge toward a model rooted in readiness, according to the service’s chief information and facts officer.
“Today, I would argue that the way that we do cybersecurity at the Office of Navy — and at the Section of Protection but that’s over my paygrade — … is completely wrong,” Aaron Weis, Navy CIO, reported at the Cloudera Government Forum. “We look at cybersecurity as a compliance trouble. And it is most definitely not a compliance challenge.”
As an alternative, the assistance requires to transfer towards a readiness product that is calculated holistically, he said.
“And when I talk about readiness, I’m not indicating it is fleet readiness … I’m expressing it is a model inspired by how we strategy readiness,” Aaron Weis, Navy CIO, mentioned at the Cloudera Government Discussion board. “Readiness is a thing that is a dynamic product … It is measured really holistically.”
Connected Distinctive: MS Groups buyers at Army Futures Command possibly exposed personal info
Cybersecurity through compliance effects in danger boosts, delayed capabilities, inadequate safety and wasted means, in accordance to Weis.
The Navy has been operating in direction of its new, holistic product given that previous November and to that conclude created a application referred to as Cyber Ready. With the software, the support would like to shift cybersecurity away from rote compliance forms and towards a “cyber ready” state that permits acquisition speed and greater defends the service’s data.
The system also seeks to “apply designs of currency so that we’re not just acquiring an ATO [authorization to operate] at the time, but you’re continuing to receive and re-earn your ATO day to day by this concept of forex,” Weis explained.
Linked: Application Keep For Warships: Within The Navy’s Challenge To Revamp How The Fleet Receives Software
In addition to the currency concept, Weis stated, there are numerous lines of effort and hard work the Navy is pursuing to shift the service to a additional holistic cybersecurity solution, including continous checking with software-driven crimson teaming and automobile-crimson teaming, acquisition changes and planning its workforce.
“And so we’re on a path. This released very last yr,” Weis explained. “We are on a initial established of sprints, a 90-working day dash, where we’re putting the meat on the bones of this thought. And we’re also actively working to recognize sets of pilots. And so we’re receiving a compact amount of pilots who are volunteering to go through this and assist us find out and it will be a hugely iterative method as we go ahead.”
Weir also laid out a few broad ambitions the Navy wishes to accomplish dependent on its 2019 Cyber Readiness Overview: modernize the service’s infrastructure, push innovation at velocity and protect the service’s info “wherever it is.”
“And notably, we did not use the term cyber. I’m of the mind that cyber is probably one of the most overused words and phrases in this city, in this field … It usually means all the things to absolutely everyone,” he stated. “And thus it form of suggests very little. So we have to set a finer place on it. We have to defend our info wherever it lives — at rest, in transit, in the industrial base, in our systems, at the tactical edge. You title it, we have to be in a position to protect it. And we have not been doing a terrific career of that in the previous as the Cyber Readiness Review articulated.”
Weis’s opinions occur as the Pentagon ramps up funding in its cyberspace actions and aims to streamline its large network infrastructure of non-provider-certain businesses.
DoD in its fiscal 2023 request wishes $11.2 billion to harden its networks, operationalize zero have faith in architecture and boost cybersecurity guidance for protection contractors. The ask for is an $800 million improve over its FY21 request.
“We’re also investing to make improvements to readiness in the nation’s cyber power by funding cyber ranges to empower training and exercise routines in the cyber area,” Vice Adm. Ron Boxall, director of force framework, methods and assessment for the Joint Team, told reporters March 29. “Finally, the budget lays the basis for US [Cyber Command] to have ownership of the mission and assets of the cyber mission force beginning in FY24 as directed in the [FY]22 NDAA.”
[ad_2]
Supply link





More Stories
Key Considerations For The Best Fleet Road Assistance
Cheap Car Auto Insurance – 5 Tips
Is the Operation Repo TV Show Real Or Fake?